As a business owner, you hear the term "small business cybersecurity solutions" a lot. But what does it actually mean? It’s not just about a single piece of software. It’s the combination of tools, a smart game plan, and the everyday habits that protect your company’s digital lifeblood from online threats. For most small and mid-sized businesses (SMBs), this boils down to a strategy called layered defense. Think of it like the multiple locks on your front door—it includes firewalls, endpoint protection, multi-factor authentication, and solid data backups to fend off common attacks like phishing and ransomware. The real challenge isn't knowing what these things are; it's figuring out how to implement them effectively without breaking the bank or hiring a full-time IT army.
Why Your Business Is a Bigger Target Than You Think

Working with businesses across Western Pennsylvania and Eastern Ohio, I hear a common refrain from owners: "We're too small to be a target." It’s an understandable assumption. When the news is filled with stories about massive corporate data breaches, it’s natural to feel like you’re flying under the radar.
But that feeling is one of the most dangerous misconceptions in business today. Cybercriminals don’t see your business as "small"—they see it as an opportunity.
To them, you’re the ideal target. You have valuable data, but you likely don’t have the massive, enterprise-level security budget of a Fortune 500 company. That combination doesn't make you a small fish; it makes you an easy, high-value prize.
The Automated Attack Landscape
Modern cyberattacks are rarely personal. Attackers use automated tools that relentlessly scan the internet for vulnerabilities, much like a car thief methodically checking every door handle in a parking lot. They aren't looking for a specific make or model; they're just looking for the easiest way in.
This automated approach means your company's size is completely irrelevant. The software is simply hunting for common weak spots, like:
- Outdated software that hasn’t been patched
- Weak or reused employee passwords
- No multi-factor authentication on critical accounts
- Unsecured remote access points
If your business has one of these weaknesses, you're on their list. It’s not a question of if an automated tool will find you, but when.
The Hard Numbers Behind the Myth
The data paints a stark picture. According to recent research, a staggering 43% of all cyberattacks globally target small businesses, and 46% of breaches hit organizations with fewer than 1,000 employees. The consequences are devastating; historical data shows that 60% of small businesses that suffer a significant cyberattack shut down within six months. You can dig deeper into these numbers by exploring more small business cyberattack statistics.
Here’s the reality: Cybercriminals often use smaller businesses as a gateway to attack their larger partners and clients, exploiting the trust built into your supply chain. Your security posture doesn't just protect your company; it protects your entire business network.
Getting this mindset shift right is the first crucial step toward effective protection. You are not too small to be a target; you are a prime target because you are a small business. Acknowledging this isn't about fear-mongering. It's about making a smart, informed decision to protect the company you’ve worked so hard to build.
Understanding Your Core Security Defenses
Cybersecurity can feel overwhelmingly complex, but its foundations are built on just a few core defenses working together. As a business owner, thinking about these defenses isn't just an IT task to delegate—it's a fundamental part of running a healthy, resilient company.
Let's make this simple. I find the best way to explain it is with a "Castle Defense" analogy. Imagine your business is a castle. Inside, you have your treasure: customer data, financial records, and proprietary information. You wouldn't just leave the main gate wide open, right? The same logic applies to your digital operations. Each security layer is just a different part of your castle's defense system.
Firewalls: The Castle Walls and Gatekeepers
Your first and most fundamental line of defense is the firewall. Just like the strong outer walls of a castle, a firewall stands between your internal business network and the open internet. Its primary job is to be a vigilant gatekeeper, inspecting every bit of digital traffic trying to come in or go out.
The firewall operates on a strict set of rules that you or your IT partner define. It’s smart enough to know which traffic is friendly (like an employee securely accessing your server from home) and which is hostile (like a known bad actor trying to find a way into your systems). It automatically blocks those unauthorized attempts, acting as your 24/7 digital sentry.
A firewall is non-negotiable for any business connected to the internet. It’s the baseline defense that prevents a huge volume of automated attacks from ever reaching your internal systems.
Without a properly configured firewall, your network is like a house with no doors or windows, making it incredibly easy for attackers to find and exploit a way in.
Essential Cybersecurity Layers for Your Business
| Security Layer | Primary Function (The 'What') | Why It's Critical (The 'Why') |
|---|---|---|
| Firewall | Acts as a digital gatekeeper, inspecting and filtering all network traffic. | It’s your first line of defense, blocking countless automated attacks and unauthorized access attempts from ever reaching your network. |
| Antivirus (AV) / EDR | Detects and neutralizes malicious software on individual devices (endpoints). | Protects your computers and servers from viruses, malware, and ransomware that might slip past the firewall, often through email or downloads. |
| Multi-Factor Auth. (MFA) | Requires a second form of verification (like a phone code) to log in. | Makes stolen passwords useless to attackers, dramatically reducing the risk of account takeovers and unauthorized access to critical systems. |
| Secure Backups | Creates copies of your critical data and stores them in a separate, secure location. | Serves as your ultimate safety net. If a disaster like ransomware hits, you can restore your data and get back to business without paying a ransom. |
This table lays out the "big four" that form the bedrock of any solid security strategy. Each piece plays a unique and indispensable role in protecting your castle from different kinds of threats.
Antivirus and EDR: The Guards on Patrol
If the firewall is your castle wall, then Antivirus (AV) and Endpoint Detection and Response (EDR) are the guards patrolling the grounds inside. These solutions are installed on every "endpoint"—a simple term for devices like your employees' laptops, desktops, and your servers. Their job is to hunt down and neutralize any threats that manage to sneak past the outer walls.
Traditional AV software works like a guard with a wanted poster. It scans files for the "signatures" of known viruses and malware and quarantines anything that matches the list. It’s good, but it can only stop threats it already knows about.
Modern EDR solutions are much smarter. Think of them as seasoned detectives who don’t just look for known criminals but also watch for suspicious behavior. EDR monitors device activity in real-time, looking for patterns that signal an attack—like a program suddenly trying to encrypt all your files (a huge red flag for ransomware). This proactive approach allows it to stop brand-new, unknown threats, not just the usual suspects. You can dig deeper into how this works in our guide to proactive endpoint security management.
Multi-Factor Authentication: The Secret Passphrase
Even the most vigilant guards can sometimes be fooled. A cybercriminal might steal an employee’s password through a phishing email, which is like them getting their hands on a key to the castle. This is where Multi-Factor Authentication (MFA) becomes your secret weapon. Simply put, MFA is like requiring a secret passphrase in addition to the key.
MFA demands that a user provide two or more verification factors to get into an account. This usually involves a combination of:
- Something you know: Your password.
- Something you have: A one-time code sent to your smartphone or generated by an authenticator app.
- Something you are: A fingerprint or facial scan.
By forcing this second piece of proof, MFA makes a stolen password practically useless to an attacker. Turning on MFA across your email, financial software, and other critical systems is one of the single most effective cybersecurity moves an SMB can make. To really wrap your head around your defenses, it's worth checking out a complete guide to security audit in network security, which helps you review all your policies and controls.
Secure Backups: The Escape Tunnels
Let’s be realistic: no defense is perfect. A determined attacker with enough time and resources might find a way to breach your walls. When a disaster like a ransomware attack actually happens, your secure backups are your lifeline. Think of them as the secret escape tunnels that lead your most precious assets—your data—to safety.
A solid backup strategy isn't just about making copies; it’s about regularly creating copies of your critical business data and storing them in a separate, secure location (ideally offsite or in the cloud). This ensures that if your primary data gets encrypted, deleted, or corrupted, you can restore everything quickly and get back to work with minimal disruption.
Without reliable backups, you are completely at the mercy of the attacker, often stuck between paying a hefty ransom or losing your business's data forever.
How to Build a Layered Security Strategy
Ever seen someone put a bank vault door on a tent? It looks tough, but it misses the point entirely. Relying on a single security tool to protect your entire business is pretty much the same thing—it creates a false sense of security while leaving other doors wide open.
In the world of cybersecurity, we talk about defense-in-depth. It’s just a formal way of saying you need multiple, overlapping layers of security. It's a fundamental shift from reacting to disasters to proactively preventing them.
Think about how you secure your home. You don’t just lock the front door and call it a day. You also lock the windows, maybe turn on an alarm system, and probably keep your most valuable items tucked away in a safe. If a burglar picks the lock on the door, the alarm still goes off. Each layer addresses a different weakness, and together, they create a defense that’s far more resilient than any single component.
Start by Identifying Your Crown Jewels
Before you can build your defenses, you have to know what you’re protecting. Every business, whether it's a manufacturing plant in Western Pennsylvania or a professional services firm in Eastern Ohio, has "crown jewels"—the data and systems that are absolutely critical to keeping the lights on.
So, what are yours? Take a few minutes to think about it. Usually, it boils down to a few key categories:
- Customer Information: Things like names, addresses, contact details, and purchase histories.
- Financial Data: All the sensitive stuff—bank account details, payroll records, and your accounting files.
- Proprietary Information: Your "secret sauce." This could be trade secrets, unique product designs, or internal processes that give you an edge.
- Operational Systems: The software and servers you need to actually do business every day, like your CRM or ERP system.
Knowing what’s most valuable tells you exactly where to focus your strongest defenses first. It’s the essential first step in building a security strategy that actually makes sense for your business.
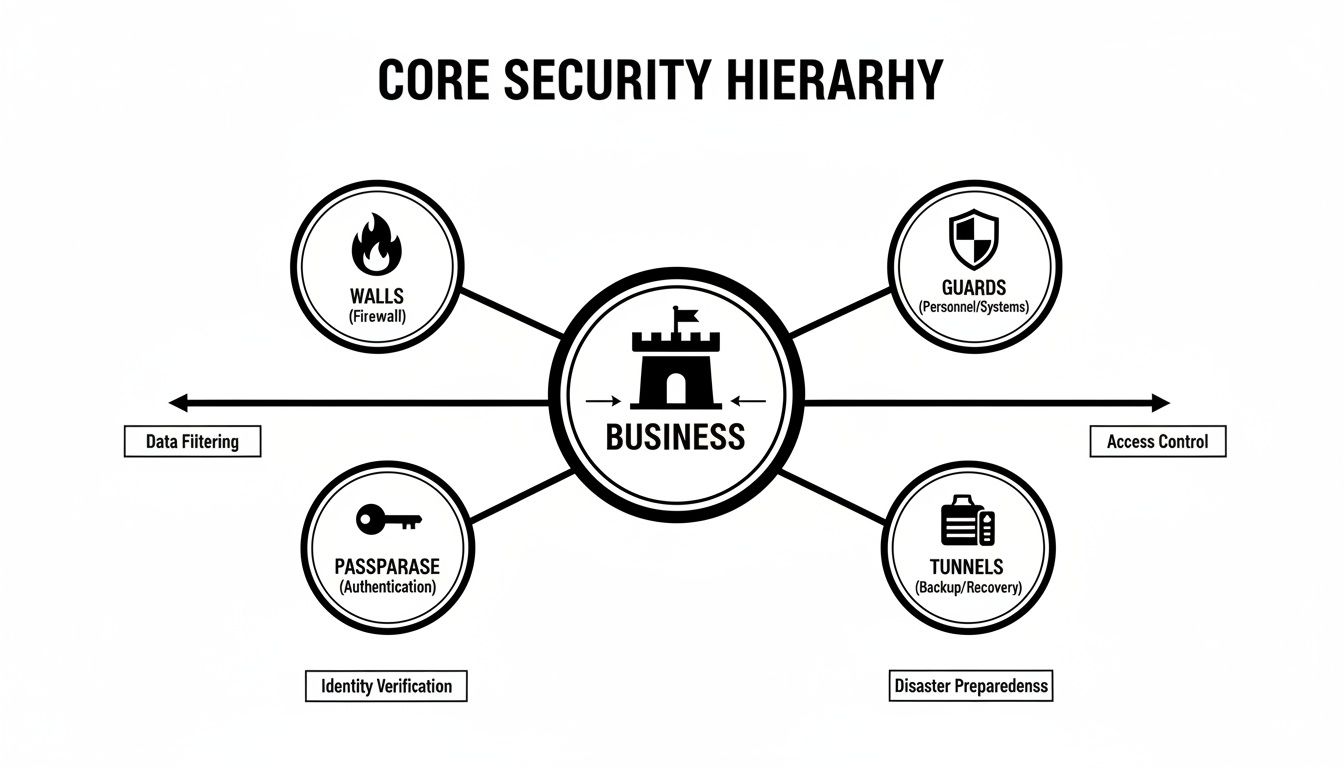
As you can see, no single layer is enough on its own. It's the combination of walls, guards, passphrases, and even escape tunnels that provides a truly complete defense.
Assembling Your Foundational Layers
With your critical assets identified, it's time to start assembling the foundational layers of your defense. This isn't about buying every flashy security product on the market. It’s about strategically putting the core tools in place that protect you from the most common threats out there.
A practical, layered approach for a small or midsize business brings a few key elements together.
The Perimeter (Network Security): Think of this as your outermost wall. It starts with a strong, business-grade firewall to filter out malicious traffic before it even gets close. This layer also includes email security filters that scan incoming messages for phishing attempts and dangerous attachments, stopping them before they land in an employee’s inbox.
The Endpoints (Device Security): Any device connected to your network is an "endpoint"—laptops, desktops, servers—and each one is a potential entry point for an attack. This layer is where modern Endpoint Detection and Response (EDR) solutions come in. They actively monitor for suspicious behavior, catching threats that old-school antivirus software would completely miss. Our experts can show you how to implement proactive endpoint security management.
The People (Human Layer): Your employees are a crucial part of your security posture, not just a liability. This layer is all about ongoing security awareness training to teach them how to spot phishing scams and follow security best practices. You reinforce this with simple but powerful policies, like enforcing strong, unique passwords and requiring Multi-Factor Authentication (MFA) on all important accounts.
A layered strategy recognizes that a threat might slip past one defense only to be caught by another. For example, an employee might accidentally click a malicious link (bypassing the human layer), but a good EDR solution will block the malware from ever running (the endpoint layer).
This defense-in-depth approach creates a security posture that is far stronger than the sum of its parts. It gives your business the resilience it needs to stand up against an ever-changing array of digital threats.
The Real Cost of a Cyberattack

It’s easy to look at cybersecurity as just another line item on the budget—an expense you try to keep as low as possible. But thinking that way misses the bigger picture. A proactive investment in small business cybersecurity solutions isn't a cost. It’s insurance against an event that could easily put you out of business.
When a security breach happens, the financial damage is so much more than the initial ransom demand or the invoice from an IT consultant. The real cost of a cyberattack is a tidal wave of direct and indirect expenses that can absolutely cripple a small business.
The Obvious and Immediate Financial Hits
Let's start with the direct costs, the ones that show up on invoices almost immediately. These are the tangible, right-in-your-face consequences of a breach that hit your cash flow hard and fast.
- Remediation and Recovery: This is the big one. You'll need to hire cybersecurity experts to figure out what happened, kick the bad guys out, and restore your systems from backups. This is emergency-rate work, and it gets expensive very quickly.
- Regulatory Fines: If your business handles sensitive information—think HIPAA for healthcare or CMMC for defense contractors—a data breach can bring on staggering fines for non-compliance.
- Legal Fees: It's not uncommon to face lawsuits from customers or partners whose data was exposed. That means costly legal battles and potential settlements.
- Ransom Payments: While security pros will always tell you not to pay, some business owners feel backed into a corner. It's a direct, unrecoverable financial loss, and there’s absolutely no guarantee you'll even get your data back.
These costs pile up in a hurry and can deliver a knockout punch to any small business's budget.
The Hidden Costs That Linger for Months
The direct costs are painful, no doubt. But it’s the indirect, hidden costs that often do the most long-term damage. These are the consequences that don't show up on an invoice but can slowly eat away at the foundation of your company.
Picture a local manufacturing facility here in Western Pennsylvania getting hit with ransomware. Their whole production line grinds to a halt because the systems that control the machinery are locked up.
The real damage isn't just the ransom. It's the days or weeks of operational downtime, the missed deadlines for key clients, the cost of paying employees who can't work, and the frantic calls to customers explaining the delays.
This is where the financial impact truly explodes. The average total cost of a cyberattack on an SMB can range from $254,445 to as high as $3.31 million. It's not surprising that after an attack, 80% of businesses report they have to spend significant time rebuilding trust. As a result, 63% of small businesses have started allocating more funds to their cyber defenses. You can dig into more of these stats in this report on the financial impact of cyberattacks on Heimdal Security.
Here are some of the most damaging hidden costs:
- Reputational Damage: Trust is the currency of business. A breach tells your customers that you can't be trusted to protect their data, and many will take their business elsewhere.
- Customer Churn: Losing the customers you already have is far more expensive than finding new ones. After a security incident, many will leave and never come back.
- Increased Insurance Premiums: If you file a claim for a cyber incident, get ready for your cybersecurity insurance premiums to skyrocket—if you can even get coverage at all.
This reframes the entire conversation. Investing in security today isn't about buying software; it’s about preventing these devastating losses tomorrow. It delivers a powerful return on investment simply by keeping your business open, running, and trusted by your customers.
Choosing the Right Cybersecurity Partner
Let’s be honest: navigating the maze of digital defense on your own is a huge ask for any small business owner. You're busy running your company. The right small business cybersecurity solutions aren't just about buying software; they’re about finding an expert partner who gets the unique pressures you’re under. This isn't just another vendor relationship—it's a partnership, and it has to be built on trust and a real understanding of where your business is headed.