As a business owner, you're constantly juggling priorities. You have customers to serve, operations to manage, and a team to lead. The last thing you have time for is becoming a full-time cybersecurity analyst. Yet, the nagging question remains: "Are we truly protected from a cyberattack?"
This is a pain point we hear every day from small and medium-sized business (SMB) leaders across Western Pennsylvania and Eastern Ohio. You've invested in foundational tools like firewalls and antivirus software, and that’s a great start. But those tools are like strong locks on your doors—they’re good at stopping common, known threats. What happens when a sophisticated intruder learns how to pick those locks or finds a vulnerability you didn't even know existed?
This is where Managed Detection and Response (MDR) comes in. Think of it as having a dedicated, 24/7 expert security team actively watching over your business. It’s a service that combines advanced technology with human expertise to continuously monitor your systems, hunt for hidden threats, and shut down attacks before they can cause real damage.
Your Proactive Defense in a Complex Threat World
Today's cyber threats are stealthy. They don't always trigger a simple antivirus alert. Instead, attackers often sneak in quietly, lurking in a network for weeks or even months—a period known as "dwell time"—waiting for the right moment to deploy ransomware or steal sensitive data. This is where the limits of traditional, automated security tools become painfully clear.
That gap is precisely what Managed Detection and Response is built to fill. It isn't just another piece of software you install and forget; it's an active, hands-on service delivered by a team of human security professionals who understand the challenges SMBs face.
MDR closes the critical gap between a security tool sending an alert and an expert taking decisive action. It shifts your security posture from reactive to proactive, focusing on hunting for threats, not just waiting for alarms.
MDR at a Glance: What It Is vs. What It Isn't
To make it even clearer, let's break down how MDR fundamentally differs from the basic security tools most businesses are used to.
| Key Feature | Managed Detection & Response (MDR) | Traditional Antivirus/Firewall |
|---|---|---|
| Approach | Proactive threat hunting & investigation | Reactive blocking of known threats |
| Human Element | 24/7 expert security analysts | Automated software alerts |
| Response | Guided & hands-on incident response | User is responsible for response |
| Focus | Detecting hidden, advanced threats | Stopping common malware & viruses |
| Visibility | Deep network & endpoint visibility | Basic device-level protection |
As you can see, MDR operates on a completely different level. It assumes a threat might already be inside and actively looks for it—a game-changer for protecting your business from modern attacks like business email compromise and ransomware.
This shift toward proactive defense is why the MDR market is booming. For many SMBs, MDR is a crucial form of outsourced cybersecurity, giving them access to threat intelligence and monitoring capabilities that were once only available to massive corporations.
To get a better handle on the basics, you can always check out our introduction to cybersecurity for small businesses.
How MDR Works: A Look Inside the Security Operations Center
So, what really happens behind the curtain after you partner with an MDR provider? It’s not about installing new software and calling it a day. It’s about activating a living, breathing cycle of protection run by a team of human experts. This team works from a Security Operations Center (SOC)—think of it as the command center for your cybersecurity defense.
At its heart, an effective MDR service follows a straightforward, methodical loop designed to find and shut down threats before they can disrupt your business. It’s the perfect blend of sophisticated technology and the kind of intuition that only comes from human experience.
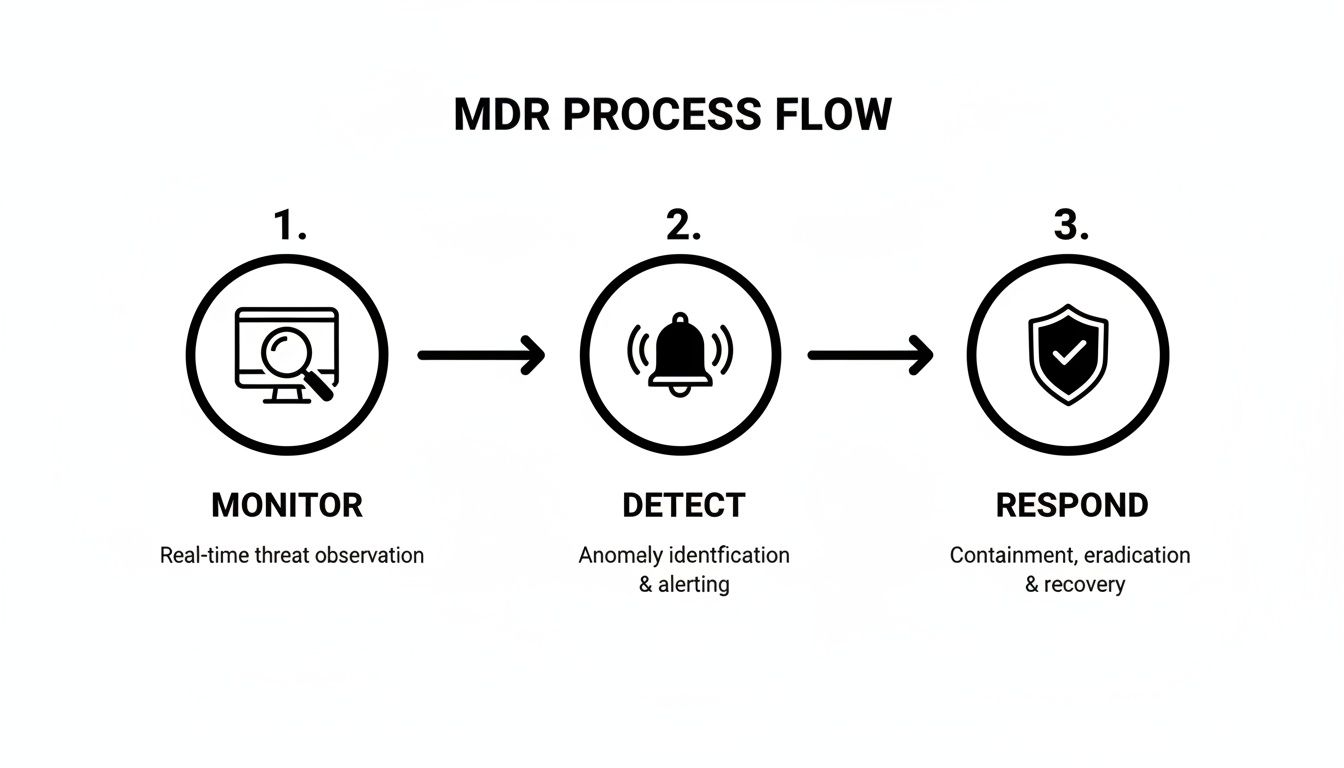
This simple, three-step engine is what drives an MDR service, protecting your business from the first hint of trouble all the way through to final resolution.
Stage 1: Proactive Monitoring and Threat Hunting
The journey starts with visibility. MDR technology is deployed across your critical systems—employee laptops, company servers, cloud applications, and more. This technology acts like a network of sensors, constantly gathering data to create a complete, real-time picture of everything happening in your IT environment.
But here’s the key difference: MDR doesn’t just sit around waiting for a blaring alarm. This is where proactive threat hunting comes into play. Security analysts, armed with up-to-the-minute global threat intelligence, actively sift through your system data. They’re looking for the subtle clues and suspicious patterns that automated tools almost always miss.
Think of it like a security guard who does more than just watch the camera feeds. They’re actively patrolling the grounds, checking locked doors, and looking for anything that feels even slightly out of place. This human-led effort is absolutely essential for catching those sneaky "low and slow" attacks designed to fly under the radar. If you’re looking to get more proactive with your defenses, our guide on endpoint security management is a great place to start.
Stage 2: Expert-Led Threat Detection
When either the monitoring technology or a threat hunter spots something suspicious, the detection phase kicks in. An alert is generated, but it doesn't just get added to a pile of notifications flooding your inbox. Instead, it goes directly to a human analyst for immediate investigation.
This is a game-changer for any SMB leader. Your team is no longer burdened with the stressful job of figuring out if an alert is a real fire or just a false alarm. The SOC analysts handle that for you. They use their expertise to:
- Investigate the context around the alert to understand the full story.
- Correlate data from different sources to connect the dots and see the bigger picture.
- Eliminate false positives, ensuring you only hear from them when there's a credible threat.
An MDR service cuts through the noise. Instead of drowning in hundreds of meaningless alerts, you get a single, validated notification about a genuine threat that actually needs your attention.
Stage 3: Guided Incident Response and Remediation
Once a threat is confirmed, the "Response" part of MDR kicks into high gear. This is where the service truly shines, turning a potential catastrophe into a controlled, manageable event. The SOC team doesn't just drop a problem in your lap; they guide you, step-by-step, through fixing it.
A core strength of MDR is its ability to provide rapid incident response the moment a threat is verified. The response process is clear and effective:
- Containment: The absolute first priority is to stop the threat from spreading. This could mean isolating an infected laptop from the network or temporarily disabling a compromised user account to slam the door on the attacker.
- Remediation: The team then provides clear, actionable instructions for your team (or ours) to completely remove the threat from your systems. No guesswork involved.
- Analysis: After the dust settles, you get a full report. It breaks down what happened, how it was stopped, and, most importantly, what steps you can take to prevent it from ever happening again.
This guided process means your business is never left to fend for itself in a crisis. You have a team of seasoned experts right there with you, providing the clear direction needed to get back to normal operations quickly and safely.
Decoding the Cybersecurity Alphabet Soup: MDR vs. MSSP vs. EDR
If you've started researching cybersecurity, you've probably waded into a sea of confusing acronyms. MDR, MSSP, EDR… they get thrown around a lot, often interchangeably. But they represent vastly different approaches to protecting your business.
Getting this right isn’t just about semantics; it’s about choosing the right defense for your company. Let’s cut through the jargon.

Endpoint Detection and Response (EDR): The Security Camera
Think of Endpoint Detection and Response (EDR) as a powerful security tool. It’s like installing high-definition cameras on every door and window of your business—your endpoints, such as laptops, servers, and phones. EDR technology records everything happening on these devices, spots suspicious movements, and gives you the footage to investigate.
However, a camera is only as good as the person watching the monitor. EDR provides incredible visibility, but it still puts the burden on your team to analyze the flood of alerts, figure out what’s a real threat versus a false alarm, and know exactly how to respond when an intruder is spotted. For a busy SMB, that’s a full-time job in itself.
Managed Security Service Provider (MSSP): The Alarm Monitoring Service
A Managed Security Service Provider (MSSP) is a broader security service. Picture this as hiring an alarm company that monitors your firewall and other security devices. They keep an eye on your perimeter, manage your security tools, push out updates, and will call you if a loud alarm goes off.
MSSPs are great for managing your security devices and filtering out basic, known threats. Their focus is often on compliance and logging. While that’s valuable, their response is typically passive. They’ll alert you to a problem, but the hands-on investigation and cleanup are usually left up to you. For a closer look at what this entails, you can explore more about what a managed service provider does on our blog.
Managed Detection and Response (MDR): The On-Site Security Team
Now we get to Managed Detection and Response (MDR). This isn't just a service; it's a highly specialized, threat-focused partnership. Forget the alarm company—this is an elite, 24/7 security team that not only watches the cameras (the EDR tool) but actively patrols your property, hunts for hidden threats, and helps you neutralize any intruders they find.
MDR combines the powerful EDR tool with a team of human experts—analysts, threat hunters, and incident responders—who manage the entire security lifecycle for you. They don’t just forward alerts; they investigate them, contain threats by isolating affected systems, and guide you through the entire remediation process. It's a hands-on, active defense built for speed and effectiveness.
Comparing Security Services: MDR vs. MSSP vs. EDR
This table highlights the key differences between these three common security solutions, helping you see where each one fits into a cybersecurity strategy.
| Attribute | Managed Detection & Response (MDR) | Managed Security Service Provider (MSSP) | Endpoint Detection & Response (EDR) |
|---|---|---|---|
| Primary Focus | Proactive threat hunting, incident response, and remediation. | Device management, log monitoring, and alert filtering. | Endpoint visibility and data collection for threat detection. |
| Type | A specialized security service. | A broad security service. | A security tool or technology. |
| Response | Active. Team investigates, contains, and neutralizes threats. | Passive. Alerts you to issues, investigation is often up to you. | Tool-based. Provides data; requires human analysis and response. |
| Core Value | Expertise and action. Delivers a security outcome. | Management and compliance. Manages security infrastructure. | Visibility and data. Provides the raw intelligence. |
| Best For | Businesses needing expert-led, 24/7 threat neutralization. | Companies needing help managing security tools and meeting compliance. | Organizations with a dedicated security team to operate the tool. |
As you can see, each plays a distinct role. While EDR is crucial technology and MSSPs offer valuable management, MDR delivers the complete, active defense that modern threats demand. For an SMB with limited internal IT staff, MDR provides access to an entire security operations team for a fraction of the cost of hiring even one in-house analyst. It’s the most practical way to defend your business against sophisticated cyberattacks.
The Real-World Business Benefits of MDR for SMBs
Let's cut through the technical jargon. Understanding what Managed Detection and Response is on paper is one thing, but what does it actually do for your business? For a small or midsize business owner in our region, every investment has to pull its weight. It's time to translate the features into real-world value for your operations, your budget, and your peace of mind.
MDR isn't just another line item in the IT budget; it’s a strategic investment in business resilience.

Ultimately, MDR directly impacts your bottom line by stopping the kinds of costly disruptions that can bring an SMB to its knees.
Drastically Reduce Business Downtime
Downtime is a killer. For any business—but especially for manufacturers, healthcare clinics, or professional service firms—every minute your systems are offline means lost revenue, blown deadlines, and fractured client trust. The number one goal of an MDR service is to shrink the time between a threat's arrival and its complete shutdown.
It all comes down to minimizing "dwell time"—that dangerous window when an attacker is hiding in your network, completely undetected. The global average for dwell time can be shockingly long, giving attackers weeks to do damage.
By combining 24/7 expert monitoring with swift, guided response, MDR transforms a potential week-long disaster into a managed incident that’s often resolved in hours. This rapid action is the single most important factor in protecting your ability to stay open for business.
Access Elite Cybersecurity Talent on an SMB Budget
Let’s be honest. Hiring just one experienced, in-house cybersecurity analyst is a six-figure investment in salary alone, not to mention benefits and training. Building a full 24/7 security team is completely out of reach for almost every SMB. This cybersecurity talent gap is one of the biggest risks businesses like yours face today.
MDR flips the script entirely. It gives your business an entire team of dedicated security experts for a predictable monthly fee—a fraction of what it would cost to hire a single person. You get:
- Expert Threat Hunters: Professionals who actively search for hidden threats before they can cause damage.
- Incident Responders: Specialists who are on standby to guide you through a crisis, step-by-step.
- Security Analysts: The eyes on the screen, investigating alerts around the clock so you don't have to.
This model makes true, enterprise-grade security affordable, leveling the playing field so your business can be just as well-defended as a Fortune 500 company.
Meet Growing Compliance and Insurance Demands
If you work in healthcare (HIPAA), manufacturing (CMMC), or handle any kind of sensitive customer data, you know compliance rules get stricter every year. At the same time, cyber insurance providers are demanding much stronger security controls before they’ll even write a policy.
An MDR service is a huge asset here. It delivers the detailed monitoring, event logging, and documented incident response procedures that auditors and insurance underwriters need to see.
- For Healthcare: MDR helps you meet HIPAA’s strict requirements for continuous network monitoring and breach response protocols.
- For Manufacturing: It provides a critical security layer needed for CMMC compliance, especially if you're in the defense supply chain.
- For Insurance: MDR clearly demonstrates proactive risk management, which can lead to better policy terms and lower premiums.
Putting MDR in place isn't just about security; it's about proving to regulators, partners, and customers that you take protecting their data seriously.
Gain True Peace of Mind
Finally, one of the most important—but often overlooked—benefits is the simple peace of mind MDR provides. As a business owner or IT leader, you already have enough on your plate without losing sleep over a potential late-night cyberattack.
Knowing you have a dedicated team of experts watching over your business 24/7/365 is invaluable. It frees you and your team to focus on what you do best: serving your customers and growing your business. Instead of constantly reacting to security alerts, you can move forward with the confidence that your most critical assets are being actively protected by a team that never sleeps.
Is Your Business Ready for MDR? Key Questions to Ask
Deciding to invest in a new security service can feel like a major step. While you hear about the benefits, it's natural to wonder, "Is this the right move for my business right now?" For many SMBs we work with in our region, Managed Detection and Response is the logical next step in their security journey, but you have to be sure.
This isn't about getting lost in complex technical specs. It's about your business reality—your risks, your resources, and what you’re trying to protect. By asking a few straightforward questions, you can get a clear picture of whether your organization has hit the point where MDR becomes a necessity.
A Practical Self-Assessment Checklist for SMBs
Take a moment to honestly assess where your business stands. If you find yourself answering "yes" to even a few of these, it’s a strong signal that MDR should be on your radar.
Do you handle sensitive client or patient data?
If you store medical records (HIPAA), financial details, or other private information, you are a prime target. A breach isn’t just a technical glitch; it's a direct threat to your reputation and a potential legal nightmare. MDR provides the active oversight needed to protect this critical data.Could your business survive a week of downtime?
Be realistic about this. For most manufacturers, professional service firms, and healthcare providers we work with, even a single day of inoperable systems is incredibly damaging. A full week? That could be catastrophic. Because MDR is built to stop attacks before they cause that level of disruption, it's a direct investment in your business continuity.Do you lack a dedicated, in-house cybersecurity expert?
Let's face it, if security falls to an IT generalist who’s already swamped—or worse, the business owner—you simply don't have the bandwidth to watch for threats 24/7. MDR gives you immediate access to a full team of security specialists for less than the cost of hiring a single in-house expert, instantly filling that critical talent gap.Are you required to meet industry compliance standards?
Regulations like HIPAA and CMMC have strict requirements for continuous monitoring and incident response. MDR provides the documented, expert-led security processes that auditors and regulators demand, helping you stay compliant and avoid crippling fines.
Addressing Common SMB Concerns
For many small business owners I talk to, the two biggest hesitations are always the same: perceived cost and the fear of a complicated setup. Let's tackle those head-on.
It’s easy to look at MDR as just another line item on the budget. The more accurate way to frame it, though, is as insurance against a far greater cost. A single ransomware incident can easily cost an SMB tens of thousands of dollars—or much more—in ransom payments, recovery efforts, and lost business.
The investment in a proactive MDR service is a fraction of the cost of a single, successful breach. It shifts your spending from reactive disaster recovery to proactive risk reduction, protecting your bottom line.
As for the setup, that’s where a trusted IT partner comes in. They should handle the entire process, from deploying the technology to fine-tuning it for your specific environment. Your team's day-to-day involvement should be minimal, allowing you to focus on your business while a 24/7 protective shield is established. The goal is to make enterprise-grade security accessible, not another burden for you to manage.